PNNL Study Targets Authentication Vulnerability of Connected Lighting Systems

July 3, 2020
The U.S. Department of Energy has released the results of a study examining authentication vulnerabilities in connected lighting systems (CLS). Particularly as emerging CLS incorporate distributed intelligence, network interfaces and sensors, they can serve as data-collection platforms that enable a wide range of valuable new capabilities as well as greater energy savings in buildings and cities. However, CLS technology is currently at an early stage of development, and its increased connectivity introduces cybersecurity risks that are new to the lighting industry and must be addressed for successful integration with other systems.
There are numerous existing frameworks and guidelines for evaluating cybersecurity vulnerability, such as the National Institute of Standards and Technology (NIST) Cybersecurity Framework, the NIST 800 series comprising more than 150 resources, the International Electrotechnical Commission (IEC) 62443 series, International Organization for Standardization 27001 and 27002, Unified Facilities Criteria (UFC) 4-010-06, and UL 2900-1. Furthermore, a variety of testing resources are widely available, including the Open Web Application Security Project (OWASP) Testing Guide. While these frameworks, guidelines, and tests may apply to CLS in whole or in part, there is currently no mandatory requirement for cybersecurity testing or certification.
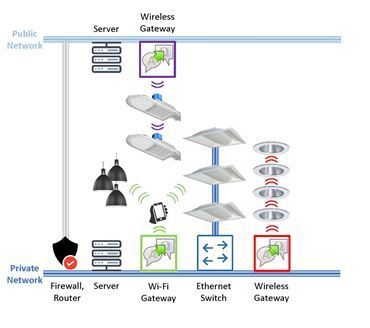
Photo: Conceptual representation of multiple connected lighting systems, showing common system architecture variations and technology implementations:
 The lighting industry, including technology developers and specification organizations, is currently evaluating the suitability of existing frameworks and guidelines for CLS. To support these efforts, the Pacific Northwest National Laboratory (PNNL) is conducting a series of studies intended to educate lighting-industry stakeholders on specific cybersecurity practices and characterize their implementation in commercially available CLS with varying system architectures, network-communication technologies, and degrees of maturity.
The lighting industry, including technology developers and specification organizations, is currently evaluating the suitability of existing frameworks and guidelines for CLS. To support these efforts, the Pacific Northwest National Laboratory (PNNL) is conducting a series of studies intended to educate lighting-industry stakeholders on specific cybersecurity practices and characterize their implementation in commercially available CLS with varying system architectures, network-communication technologies, and degrees of maturity.
The first study explores authentication practices and their implementation in multiple CLS. A total of 18 tests were developed by UL and implemented in PNNL’s Connected Lighting Test Bed (CLTB). The tests explore the implementation of basic authentication best practices as well as known technology-specific best practices. As a result, not all tests are applicable to all CLS.
A total of 40 out of 72 potential tests (4 CLS, 18 potential tests each) were applicable for 4 evaluated CLS, and the CLS collectively passed 26 of the 40 tests (65%). While pass/fail ratio is a simple way of reporting test results, it is not really a relevant metric. Cybersecurity vulnerability testing is a risk-analysis practice; the relevance of passing or failing a certain test is best evaluated in concert with an understanding of the risk associated with that vulnerability in a specific implementation. Nevertheless, pass/fail ratios give some indication of the range of performance found in market-available CLS.
Based on the limited results of this study, it appears that the CLS being brought to market have varying levels of authentication vulnerability. It is hoped that these evaluations will support and perhaps accelerate industry discussions on the risks of specific security vulnerabilities, what vulnerabilities should be addressed by lighting-specific best practices in development, and whether any such practices should be included in voluntary lighting standards.
PNNL plans to conduct more authentication testing and to work with UL and other cybersecurity experts to explore authorization vulnerabilities. PNNL will bring these results to the ANSI C137 Lighting Systems ad-hoc working group focusing on cybersecurity vulnerability, for consideration in the creation and development of new standards.
Go HERE for the report.
Craig DiLouie, LC, is Education Director for the Lighting Controls Association. Reprinted with permission of the Lighting Controls Association, www.lightingcontrolsassociation.org









